FIPS + Qubes-OS
npub1rmz9gu6de0m0u4ysrn39crrud099ahvfgs6pvasl4hpjr5ud7yus54xv06
hex
b89aaef8306f38f97d502a4020ae5d6cd45cbfeee0a45c3c3613b3bf54b5f3e3nevent
nevent1qqst3x4wlqcx7w8e04gz5spq4ewke4zuhlhwpfzu8smp8val2j6l8ccprpmhxue69uhhyetvv9ujuem4d36kwatvw5hx6mm9qgspa3z5wdxuhah72jgpecjup37xhjj7mky5gdqkwc06msep6wxlzwgzpmwf9Kind-1 (TextNote)
FIPS + Qubes-OS
GM.
Yesterday I integrated FIPS into Qubes-OS. Here is a short description of what each of them does, and the resulting setup.
FIPS - a permissionless internet.
To get a domain name, you need ask for permission. To get https, you need to ask for permission. To get an IP address, (the final boss) you need to ask for permission.
FIPS is a permissionless internet. You use a nostr address instead of an ip address, and through some cool engineering, you get a permissionless internet.
So for example: http://npub1crpldvy49ef8z34wlacwujnfudy4nd7k96aqdx5wgn6ckztz7z8q9t59ud.fips/ gets you to my web page if you are running FIPS, and you don't need permission, and neither do I.
We just need nostr addresses.
QUBES-OS - the securest OS.
Running agents locally can be a real security issue which is originally why I switched to Qubes-OS. Qubes-OS lets you run several operating systems on one machine, and encloses them in what are called "qubes". You can run whatever OS you want in each qube, all on the same machine, all securely separated and isolated.
You can also route internet THROUGH a qube. So a nice example is setting up your vpn in a qube, and use it like the following:

It forces everything you run in Debian to pass through the vpn qube, else no internet.

You can send multiple OSs through the vpn.
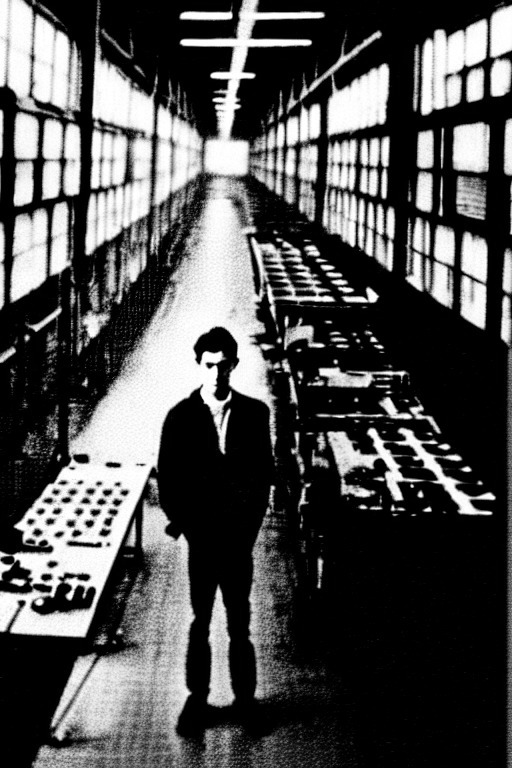
Turns out you can also create a FIPS qube. That is what I did yesterday, and part of my setup now looks something like this:

You can check out FIPS here: https://github.com/jmcorgan/fips Qubes OS here: https://www.qubes-os.org/ Follow FIPS here: nostr:npub1y0gja7r4re0wyelmvdqa03qmjs62rwvcd8szzt4nf4t2hd43969qj000ly Follow the FIPS creators here: nostr:npub19wavu4f7l6l43h24jyskn7fvzy37kcfp67aqjtmv2qgy4lp34nhsda8p6k nostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr
If you are going to attempt to do this, point your agent to this repo and it should save you some tokens. There were some gotchas that it took a long time for Claude and Codex to figure out. https://git.laantungir.net/laantungir/fips_setup
Raw JSON
{
"kind": 1,
"id": "b89aaef8306f38f97d502a4020ae5d6cd45cbfeee0a45c3c3613b3bf54b5f3e3",
"pubkey": "1ec454734dcbf6fe54901ce25c0c7c6bca5edd89443416761fadc321d38df139",
"created_at": 1775993181,
"tags": [
[
"p",
"23d12ef8751e5ee267fb6341d7c41b9434a1b99869e0212eb34d56abb6b12e8a"
],
[
"p",
"2bbace553efebf58dd55912169f92c1123eb6121d7ba092f6c50104afc31acef"
],
[
"p",
"bbb5dda0e15567979f0543407bdc2033d6f0bbb30f72512a981cfdb2f09e2747"
]
],
"content": "FIPS + Qubes-OS\n\n\nGM.\n\n\nYesterday I integrated FIPS into Qubes-OS. Here is a short description of what each of them does, and the resulting setup.\n\n\nFIPS - a permissionless internet.\n\n\nTo get a domain name, you need ask for permission. \nTo get https, you need to ask for permission.\nTo get an IP address, (the final boss) you need to ask for permission.\n\n\nFIPS is a permissionless internet. You use a nostr address instead of an ip address, and through some cool engineering, you get a permissionless internet.\n\n\nSo for example:\nhttp://npub1crpldvy49ef8z34wlacwujnfudy4nd7k96aqdx5wgn6ckztz7z8q9t59ud.fips/ \ngets you to my web page if you are running FIPS, and you don't need permission, and neither do I.\n\n\nWe just need nostr addresses. \n\n\nQUBES-OS - the securest OS.\n\n\nRunning agents locally can be a real security issue which is originally why I switched to Qubes-OS. Qubes-OS lets you run several operating systems on one machine, and encloses them in what are called \"qubes\". You can run whatever OS you want in each qube, all on the same machine, all securely separated and isolated.\n\n\nYou can also route internet THROUGH a qube. So a nice example is setting up your vpn in a qube, and use it like the following:\n\n\nhttps://blossom.laantungir.net/bb33189c1dd556583f3f606946d16a0b0cd99ba57f4c0a0492405742f47e2f05.png\n\n\nIt forces everything you run in Debian to pass through the vpn qube, else no internet.\n\n\nhttps://blossom.laantungir.net/913a045d6710bf593ead0265eeb580822a7677bd69943e88824e9e3bc7254f65.png\n\n\nYou can send multiple OSs through the vpn.\n\n\nTurns out you can also create a FIPS qube. That is what I did yesterday, and part of my setup now looks something like this:\n\n\nhttps://blossom.laantungir.net/be6c13151170d637e3a43dcbd0ef15c66d67e59e594520a39195e05e137eefd7.png\n\n\nYou can check out FIPS here: https://github.com/jmcorgan/fips\nQubes OS here: https://www.qubes-os.org/\nFollow FIPS here:\nnostr:npub1y0gja7r4re0wyelmvdqa03qmjs62rwvcd8szzt4nf4t2hd43969qj000ly\nFollow the FIPS creators here:\nnostr:npub19wavu4f7l6l43h24jyskn7fvzy37kcfp67aqjtmv2qgy4lp34nhsda8p6k\nnostr:npub1hw6amg8p24ne08c9gdq8hhpqx0t0pwanpae9z25crn7m9uy7yarse465gr\n\n\nIf you are going to attempt to do this, point your agent to this repo and it should save you some tokens. There were some gotchas that it took a long time for Claude and Codex to figure out.\nhttps://git.laantungir.net/laantungir/fips_setup",
"sig": "e954fd972e97afadec257ec4d86cedcd912a2e195454913a7cd2e2ea0066a5d3a24b9553a0ec4a8c4ffbe1745cc37d927741cab054a925d4fdc611664cd4c94c"
}